Your Couch Is Not a Fortress. Securing Remote Work Before It Secures Your Fate.
Your team is working from home in pajama bottoms and zero security here's everything that can go wrong, and how to stop it.

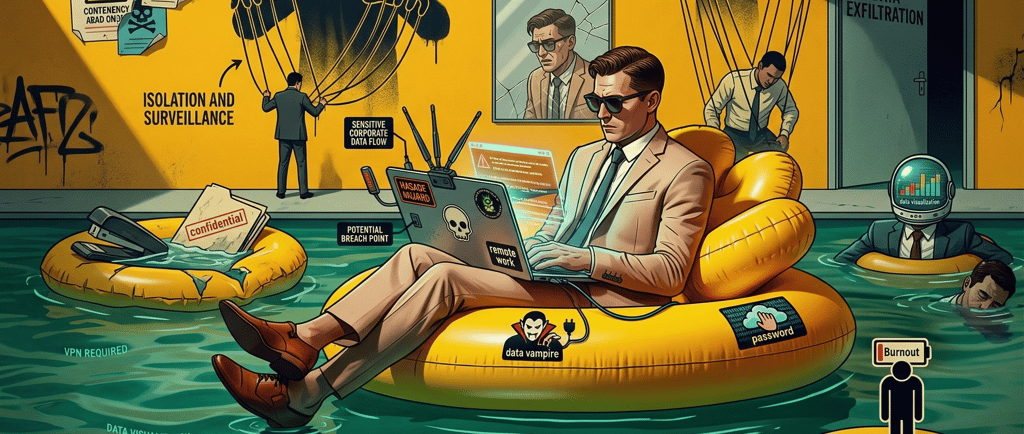
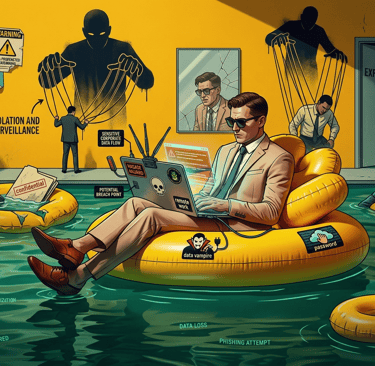
Somewhere right now, one of your employees is on a video call wearing a blazer on top and SpongeBob shorts on the bottom, connected to a café Wi-Fi network called "FREE_INTERNET_NO_VIRUS" — with your company's entire client database one stolen session away from the dark web.
Remote work is great. Remote work without security is a data breach wearing sweatpants.
This Isn't Hypothetical. It Already Happened.
In 2020, Twitter suffered one of the most embarrassing breaches in tech history. Hackers didn't find some brilliant zero-day exploit. They simply called remote employees, pretended to be IT support, and talked them into handing over their credentials. Within hours, the attackers had access to the internal admin panel and were tweeting Bitcoin scams from the accounts of Elon Musk, Barack Obama, and Apple. The total damage? Millions in losses, a destroyed reputation, and several arrests — none of which helped Twitter undo the headlines.
Then there's the Heathrow Airport incident. An employee lost an unencrypted USB stick on the street. A random passerby picked it up, plugged it in, and found themselves staring at the Queen's travel security routes, CCTV locations, and restricted area maps. All because someone couldn't be bothered to encrypt a thumb drive.
These aren't cautionary tales from some obscure corner of the internet. These are global organizations with massive security budgets. Your 20-person team working from kitchen tables and co-working spaces? The risk is the same — the budget to recover from it isn't.
Nine Ways Your Remote Team Is Probably Exposed Right Now
1. The Wi-Fi Roulette 🌐
Public Wi-Fi is not the internet with a friendly smile. It's an open channel where anyone with basic tools can intercept traffic, steal session cookies, and watch credentials fly by in plain text. That "Starbucks_Guest" network your employee is connected to might not even belong to Starbucks — attackers regularly set up fake hotspots with familiar names and wait for people to connect.
The fix: Use a VPN. Always. If your company doesn't provide one, that's a problem MSPE can solve in a day.
2. The Unattended Laptop 👀
Your employee steps away from their laptop at a café "just for a second" to grab their order. That second is all it takes. A shoulder surfer has already seen the screen. A more ambitious thief walks out with the device entirely. Congratulations — your client data is now someone else's problem.
The fix: Lock the screen every time you walk away. No exceptions. Windows + L. Command + Control + Q. Tattoo it on the inside of your eyelids if you have to.
3. The Accidental Broadcast 🕵️
Working from a coffee shop and taking a client call on speaker? Discussing project details in an airport lounge? Every person within earshot just became an unauthorized recipient of your company's confidential information. Social engineers don't always work behind a keyboard — sometimes they just sit at the next table and listen.
The fix: Sensitive conversations happen in private spaces. If you're in public, use a headset, keep your voice down, and save the details for when you're somewhere secure.
4. The Unlocked Screen 🔒
An unlocked, unattended device isn't a minor oversight — it's an open invitation. Anyone who walks by has full access to your email, your files, your Slack, and every system your browser is logged into. It takes less than 30 seconds to install a keylogger or forward a mailbox.
The fix: Set auto-lock to activate after 60 seconds of inactivity. If your team thinks that's annoying, ask them how they'd feel about explaining a breach to a client.
5. The Password That's Not Really a Password 🗝️
"Company2026." "Welcome1." "MrWhiskers." Your employee thinks their password is fine because it has a capital letter and a number. An attacker's brute-force tool cracks it in under four seconds. That's not an exaggeration — it's a benchmark.
The fix: Use a password manager that generates and stores unique, complex passwords for every account. We wrote an entire post about this — stop emailing passwords while you're at it.
6. The Phishing Email That Arrives at 6 PM 🎣
Attackers love targeting remote workers after hours. Why? Because at 6 PM, your employee is tired, distracted, and less likely to scrutinize an email before clicking. Phishing success rates spike outside of business hours — when there's no colleague at the next desk to say "hey, does this look weird to you?"
The fix: Build awareness that phishing doesn't respect office hours. If an email feels urgent at an odd time, that's exactly when it deserves more scrutiny, not less.
7. The Work Laptop That Doubles as a Family Entertainment Center 🎭
When your employee's kid uses the work laptop to download a "free Minecraft mod," your company inherits whatever malware came bundled with it. When your employee browses personal sites on a work device, every tracking cookie and compromised ad network gets a direct line into your corporate environment.
The fix: Work devices are for work. Personal devices are for everything else. This boundary isn't about being strict — it's about keeping your attack surface from doubling overnight.
8. The Mystery Download 📥
This one ties back to our first blog post, but it's worth repeating in the remote work context. Without IT sitting down the hall, remote employees are more likely to install random tools, browser extensions, and "productivity apps" without checking if they're safe. Each one is a potential backdoor.
The fix: Maintain an approved software list and make it easy for employees to request new tools through proper channels. If asking IT is harder than just downloading something, people will always take the shortcut.
9. The Oversharing Problem 💳
Working remotely blurs the line between personal and professional. Employees respond to what they think is an HR email with personal details. They share financial information over unverified calls. They click on "verify your identity" links without checking the sender. The isolation of remote work makes people more vulnerable to social engineering — there's no one around to raise an eyebrow.
The fix: Simple rule: legitimate organizations never ask for sensitive information via email or unexpected phone calls. When in doubt, verify through a known channel. Always.
The Uncomfortable Truth About Remote Security
Most companies adopted remote work overnight in 2020 and never went back to properly secure it. The VPN was "temporary." The BYOD policy was "we'll figure it out later." The security training was a single email that nobody read.
Later is now. Attackers have had years to refine their approach to targeting remote workers, and they've gotten very good at it. The question isn't whether your remote setup has gaps — it's how many, and whether you'll find them before someone else does.
Let MSPE Close the Gaps
We help businesses secure remote work the right way — not with a checklist and a prayer, but with the right combination of tools, policies, and training tailored to how your team actually operates. VPN configuration, endpoint protection, device management, secure access policies, and ongoing awareness training — all built around your environment, your budget, and your risk profile.
No single vendor. No one-size-fits-all package. Just the right solution for the way your team works.
Want to find out how exposed your remote workforce really is? Reach out at info@mspe.pro — we'd rather you hear it from us than from a breach notification.
MSPE — Unlocking the Power of Choice. Managed IT & Cybersecurity Services for SMBs, Schools, Law Firms & Charities.


